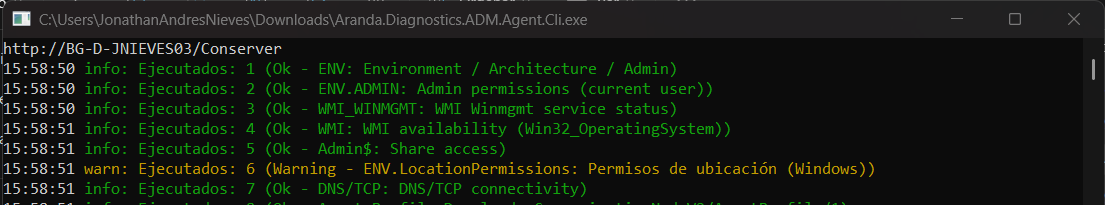
This functionality allows a diagnosis of the ADM modules, required for the operation of the agent; includes communication tests to the ADM site, site and local communication ports, verification of permits and status of the services required in the equipment, for the operation of the modules. To perform the self-diagnosis process, perform the following steps:
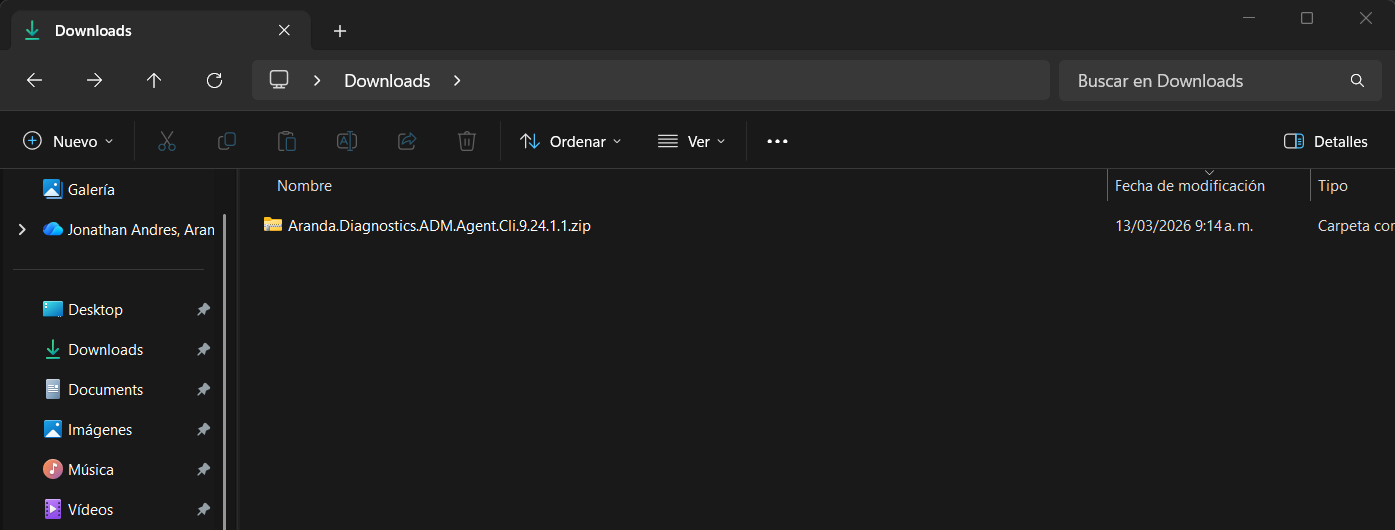
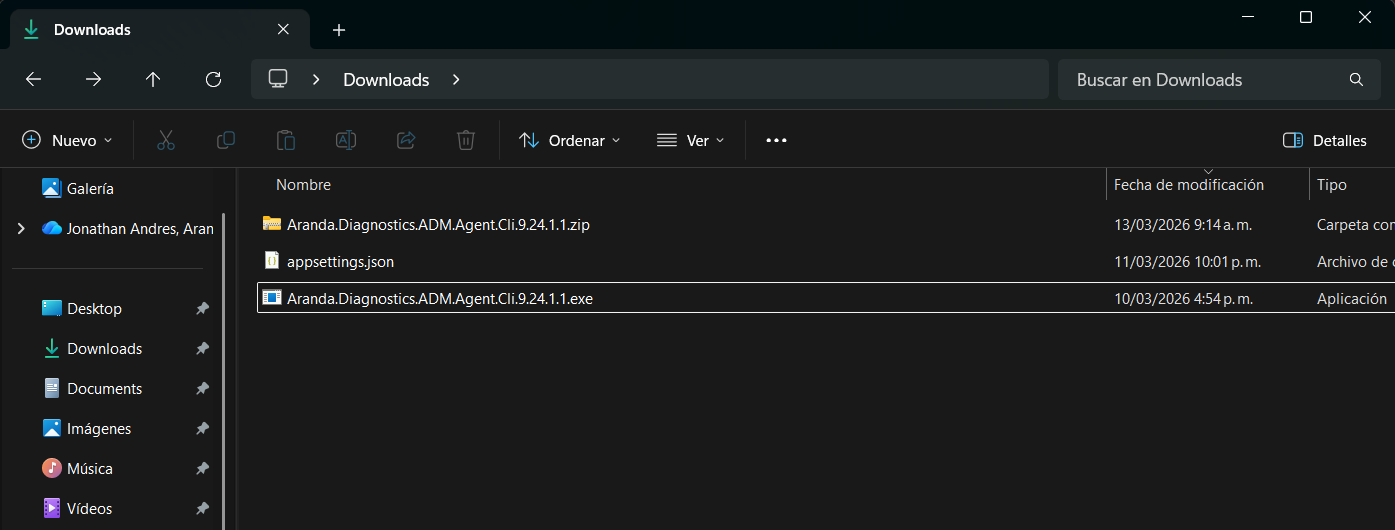
1. Download and save the package Aranda.Diagnostics.ADM.Agent.9.x.x.x.zip on a specific route, unzip it. You will be able to view the files: appsettings.json and Aranda.Diagnostics.ADM.Agent.9.x.x.x.exe.
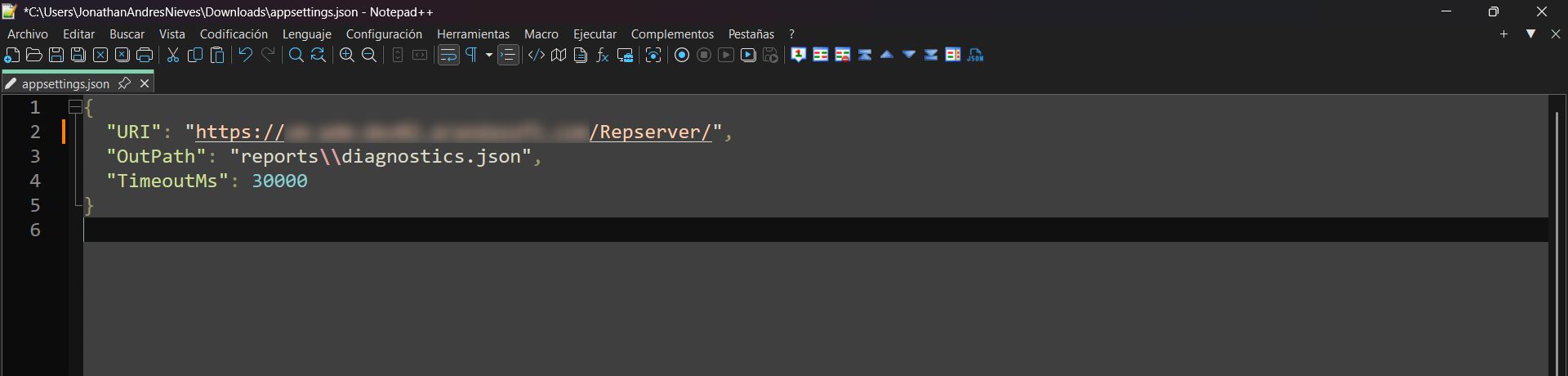
2. Modify the file appsettings.json on line two URI by the URL of the node, where the agent points or will point.
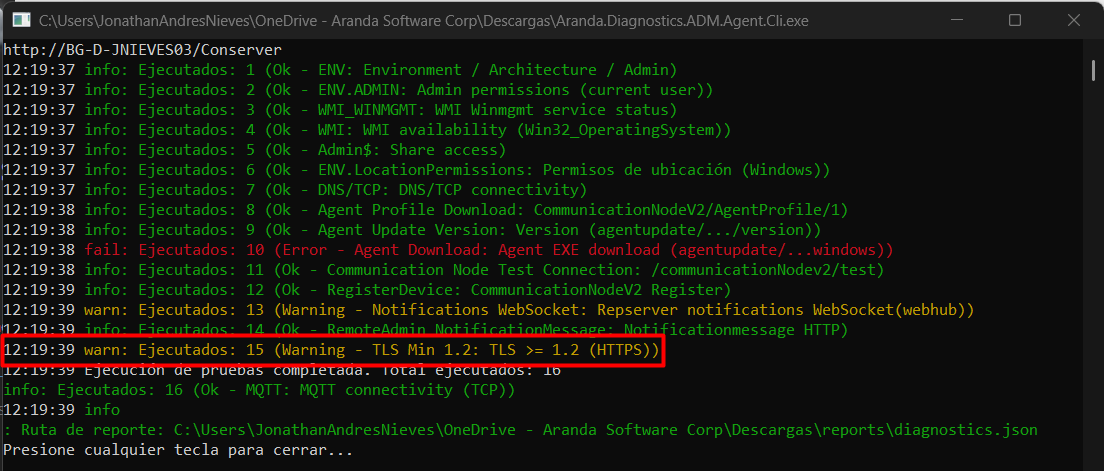
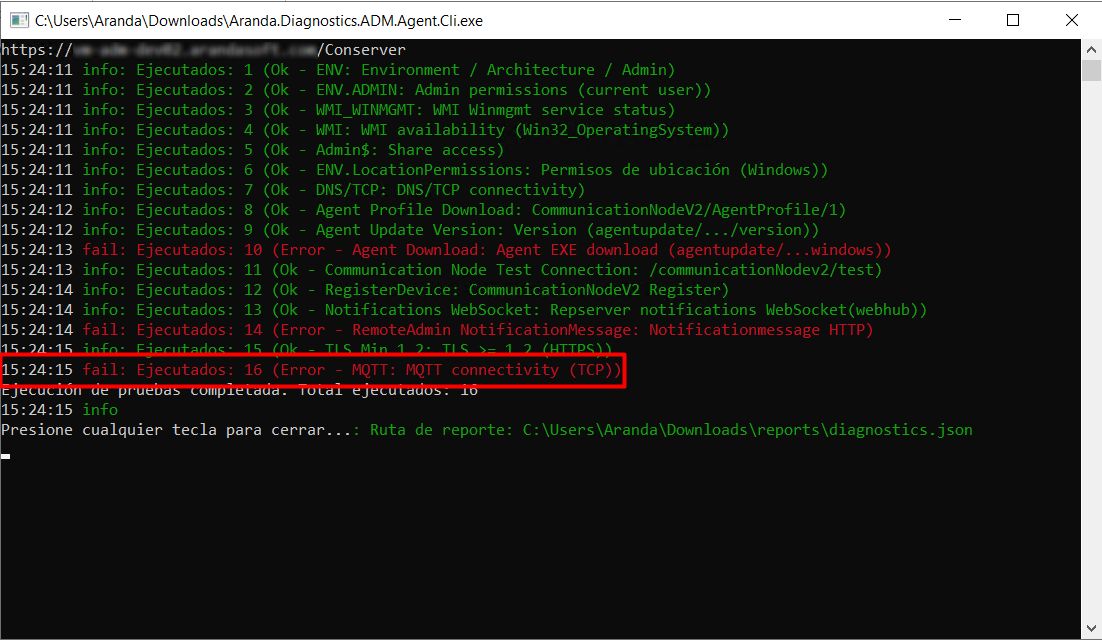
3. Run the file as administrator Aranda.Diagnostics.ADM.Agent.Cli.exe; Once executed, the utility vehicle performs the tests of architecture, services, accesses, permits, communication ports.
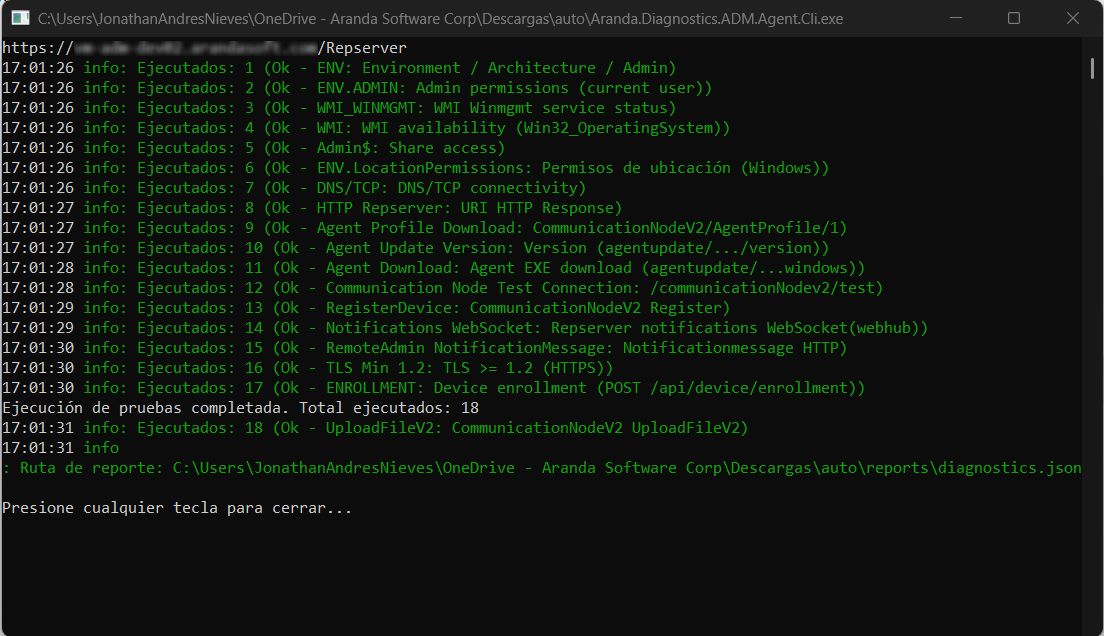
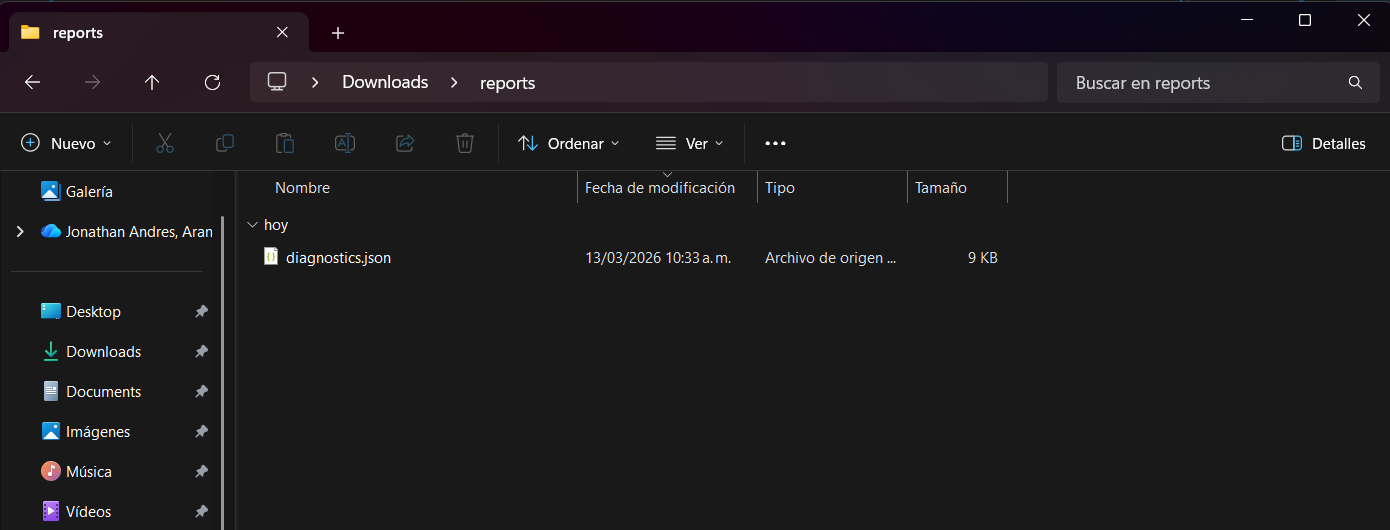
4. Once the diagnostic process is complete, close the window by pressing any key or manually closing the window. The test result is stored in the utility path, in the Reports, the file is saved diagnostics.json and you will be able to view it in an available text editor.
Resulting file
Explanation of each test performed by the self-diagnostic agent and possible errors
Below is the context and explanation of each test performed by the self-diagnosis tool. In addition, the possible errors that may occur in each test due to some local restriction in firewall, antivirus or network problems or lack of any configuration in the console are explained:
1. Equipment architecture verification
Verification of operating system architecture and folders Program Files
{
"TestId": "ENV",
"Group": "Environment",
"Name": "Environment / Architecture / Admin",
"Status": "Ok",
"Findings": [],
"Evidence": {
"OSArchitecture": "X64",
"ProcessArchitecture": "X64",
"ProgramFiles": "C:\\Program Files",
"ProgramFilesX86": "C:\\Program Files (x86)",
"IsElevated": "True"
}
}
2. Checking admin permissions
Performs a check on the user who is running the utility in order to verify if the user belongs to the administrators group.
{
"TestId": "ENV.ADMIN",
"Group": "Environment",
"Name": "Admin permissions (current user)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"User": "DOMAIN\\USER",
"IsInAdministratorsGroup": "True",
"IsElevated": "True"
}
}
3. WMI Service Verification
An enquiry is made to the service Windows Management Instrumentation (Winmgmt) checking if it is enabled and running.
{
"TestId": "WMI_WINMGMT",
"Group": "Environment",
"Name": "WMI Winmgmt service status",
"Status": "Ok",
"Findings": [],
"Evidence": {
"ServiceName": "Winmgmt",
"DisplayName": "Instrumental de administración de Windows",
"Status": "Running"
}
}
Example of error:
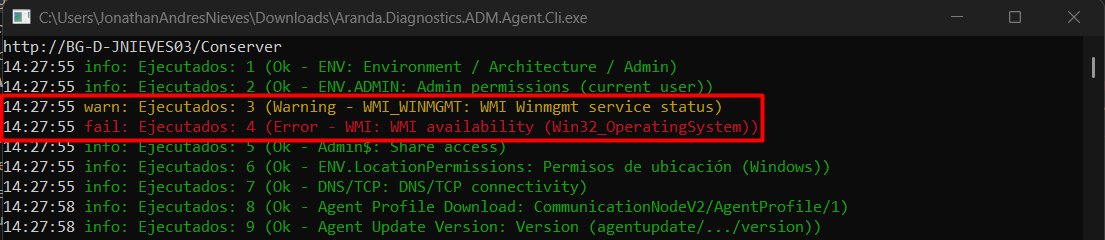
This error is caused by a service failure Windows Management Instrumentation (Winmgmt); Check if the service is enabled and started and is not blocked by a domain policy.
4. Query using the WMI service
A basic query is made requesting the editing of the operating system, version and architecture.
{
"TestId": "WMI",
"Group": "Environment",
"Name": "WMI availability (Win32_OperatingSystem)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"TimeoutMs": "30000",
"Query": "SELECT Caption, Version, OSArchitecture FROM Win32_OperatingSystem",
"OS.Caption": "Microsoft Windows 11 Enterprise",
"OS.Version": "10.0.26200",
"OS.OSArchitecture": "64 bits"
}
}
Example of error:

The most common causes for this error can be:
- The service Windows Management Instrumentation (Winmgmt) is enabled, but you do not have permissions on the Control WMI, contact your administrator to assign permissions to the user.
- Firewall-level blocking for the port used by WMI.
- Corrupt or non-existent namespace from the Control WMI
- DCOM disabled for the computer from the Component Services
5. Verify the ADMIN$ share
It is validated in a query, if on the shares, there is the ADMIN$ resource that has access to the C:Windows path or if there is a domain policy that blocks access to this resource.
{
"TestId": "Admin$",
"Group": "Environment",
"Name": "Share access",
"Status": "Ok",
"Findings": [],
"Evidence": {
"TargetHost": "DEVICENAME",
"AdminSharePath": "\\\\DEVICENAME\\Admin$",
"FileCount": "40"
}
}
Example of error:
The most common causes for this error can be:
- The resource is restricted from access by using the following AutoShareWks=0 registration key:
- Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters
- The resource is not shared from the Team Manager > Shared Folders > Shares
6. Geolocation Service Verification and Location Permissions
A consultation is made to the Geolocation Service (LFSVC) verifying if it is enabled and executing; It also checks to see if there’s a domain policy blocking location services.
{
"TestId": "ENV.LocationPermissions",
"Group": "Environment",
"Name": "Permisos de ubicación (Windows)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Location.Service": "Running",
"Location.PolicyBlocked": "False",
"Consent.Result": "Allow",
"Consent.Source": "None",
"Location.BlockReason": "None"
}
}
Example of error:
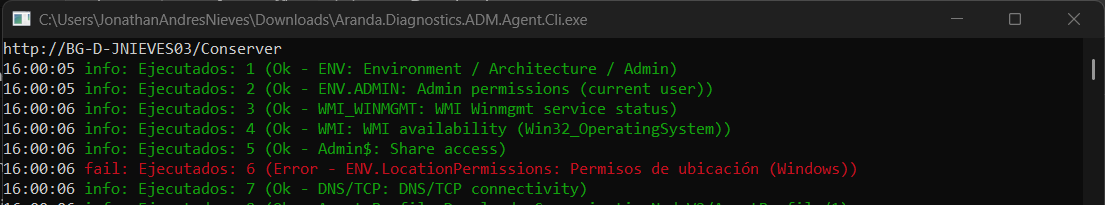
The most common causes for this error can be:
- The Geolocation Service (LFSVC) It is not enabled or has access restrictions by domain policy.
- You have domain policies configured with location access restriction. If any of these registry keys are created with DWORD = 1, they must be deleted:
- Registry Key: Software\Policies\Microsoft\Windows\LocationAndSensors\DisableLocation
- Registry Key: Software\Policies\Microsoft\Windows\LocationAndSensors\DisableSensors
- Registry Key: Software\Policies\Microsoft\Windows\LocationAndSensors\DisableWindowsLocationProvider
7. DNS/TCP Verification
A TCP connectivity test is performed to the host and port configured in the file appsettings.json checking if it performs a DNS resolution and capturing response times.
{
"TestId": "DNS/TCP",
"Group": "Prerequisites",
"Name": "DNS/TCP connectivity",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Url": "https://DNS-NAME/Repserver",
"Scheme": "https",
"Host": "DNS-NAME",
"Port": "443",
"ResolvedIPs": "IP-DETECTED",
"TimeoutMs": "30000",
"ConnectedIP": "IP-DETECTED"
}
}
8. HTTP verification to the supplied base URL
HTTP response verification is performed to the supplied base URL to confirm if it responds correctly, capturing response times.
{
"TestId": "HTTP Repserver",
"Group": "Prerequisites",
"Name": "URI HTTP Response",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Url": "https://DNS-NAME/Repserver",
"Method": "HEAD",
"StatusCode": "200",
"ElapsedMs": "380"
}
}
Example of error:
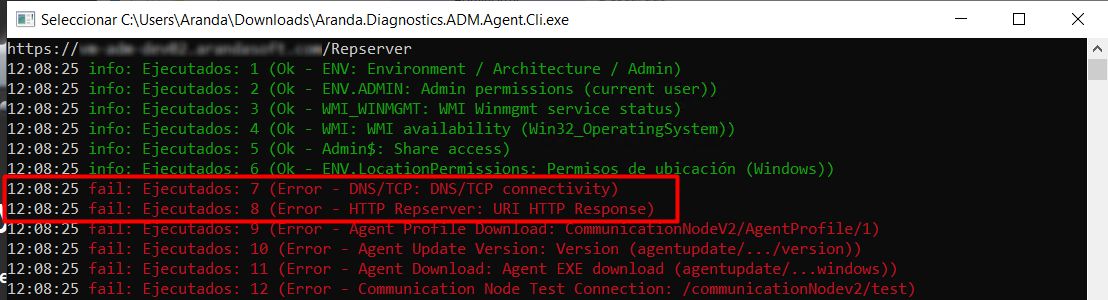
In this case, items 7 and 8 share the same scenario, due to a possible restriction of communication to the URL to which the test is being performed. Validate if it has an Internet outlet, review the network restrictions configured at the firewall level, and make the exception to the node URL.
9. Verification download of default agent profile
A query is made to the URL where the agent’s profile is stored, returning the information in JSON format with the configurations that are available for the default profile and capturing the response times.
{
"TestId": "Agent Profile Download",
"Group": "Inventory.AgentProfileDownload",
"Name": "CommunicationNodeV2/AgentProfile/1",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Url": "https://DNS-NAME.com/Repserver/CommunicationNodeV2/AgentProfile/1",
"HeadStatusCode": "200",
"HeadElapsedMs": "368",
"HeadContentType": "",
"HeadContentLength": "867",
"Head": "Ok",
"Method": "GET",
"StatusCode": "200",
"ElapsedMs": "245",
"ContentType": "application/octet-stream",
"BodyPreview": "{\"aam\":{\"aamInventory\":{\"period\":86400,\"startTime\":1772799960},\"aamInventoryLogon\":false,\"aflIncremental\":null,\"aflInventory\":null,\"excludedFiles\":[],\"excludedPaths\":[\"C:\\\\Program Files\",\"C:\\\\Program Files (x86)\",\"C:\\\\Windows\"],\"executablesToScan\":[\"EXE\",\"CPL\",\"RUN\",\"BIN\",\"PY\",\"SH\",\"BASH\"],\"extensionToScan\":null,\"synchronization\":{\"period\":600,\"startTime\":1774366188}},\"additionalSurveyFields\":null,\"apm\":{\"apmInventoryLogon\":false,\"inventory\":{\"period\":86400,\"startTime\":1772820000},\"synchronization\":{\"period\":86400,\"startTime\":1774366188}},\"apwm\":null,\"ars\":null,\"asd\":{\"synchronization\":{\"period\":600,\"startTime\":1774366188}},\"asm\":null,\"communication\":{\"fileSharing\":{\"download\":1024,\"port\":0,\"retention\":1,\"type\":4,\"upload\":1024},\"port\":9025,\"registerPeriod\":5,\"serverAddress\":[\"https:\\/\\/DNS-NAME\\/repserver\"]},\"profile\":1,\"showIcon\":true}"
}
}
Example of error:
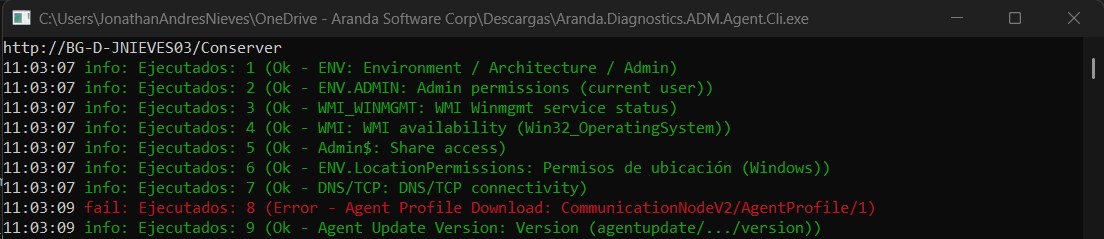
When pointing to a Conserver, they are presented by the absence of the resource in the Conserver’s file storage path. You can run the self-test again so that it runs correctly. On the first execution that fails, the Conserver processes the task that requests the resource and stores it.
10. Verification to the available version of the ADM agent
A query is made to verify the latest available version of the ADM agent and displays the available file name, identifier, download date, and captures the response time.
{
"TestId": "Agent Update Version",
"Group": "Inventory.AgentUpdate",
"Name": "Version (agentupdate/.../version)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"BaseUrl": "https://DNS-NAME/Repserver",
"Url": "https://DNS-NAME/Repserver/api/agentupdate/com.arandasoft.adm.agent.windows/version",
"Method": "GET",
"StatusCode": "200",
"ElapsedMs": "2450",
"ContentLength": "184",
"BodyPreview": "{\"fileName\":\"Aranda.Agent.Windows.x86_x64.9.24.1.4.exe\",\"installerIdentifier\":\"com.arandasoft.adm.agent.windows\",\"modificationDate\":\"2026-03-19T00:00:32.32+00:00\",\"version\":\"9.24.1.4\"}"
}
}
Example of error:
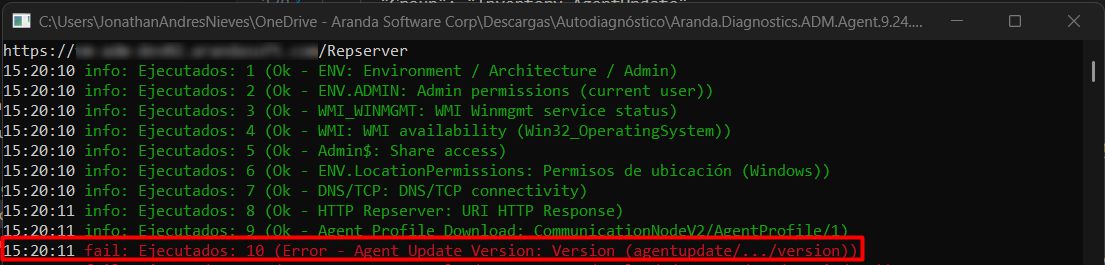
There is no version data available because the task that is responsible for downloading this information has not been executed. For more information, see Deploying Agents.
11. Agent Installer Verification
A query is performed to verify that the ADM agent’s .EXE resource exists on the storage path configured for the node being queried.
{
"TestId": "Agent Download",
"Group": "Inventory.AgentUpdate",
"Name": "Agent EXE download (agentupdate/...windows)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Url": "https://DNS-NAME/Repserver/api/agentupdate/com.arandasoft.adm.agent.windows",
"Method": "GET(Range 0-0)",
"StatusCode": "206",
"ElapsedMs": "244",
"ContentType": "application/octet-stream",
"ContentLength": "1"
}
}
Example of error:
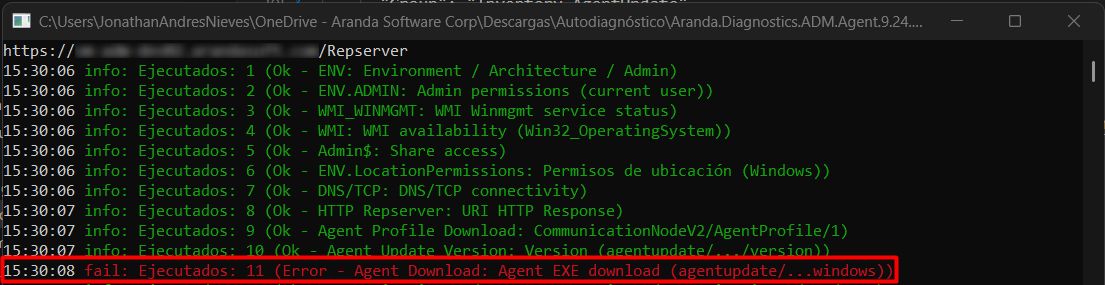
This is due to the absence of the resource in the file container for the Repserver case or in the file storage path for the Conserver case.
12. Node Connectivity Test
Connectivity test is performed to the node that was configured in the file appsettings.json and it is verified that the node is responding appropriately.
{
"TestId": "Communication Node Test Connection",
"Group": "Inventory.CommunicationNodeCnx",
"Name": "/communicationNodev2/test",
"Status": "Ok",
"Findings": [],
"Evidence": {
"BaseUrl": "https://DNS-NAME/Repserver",
"Url": "https://DNS-NAME/Repserver/communicationNodev2/test",
"Method": "GET",
"StatusCode": "200",
"ElapsedMs": "227"
}
}
Example of error:
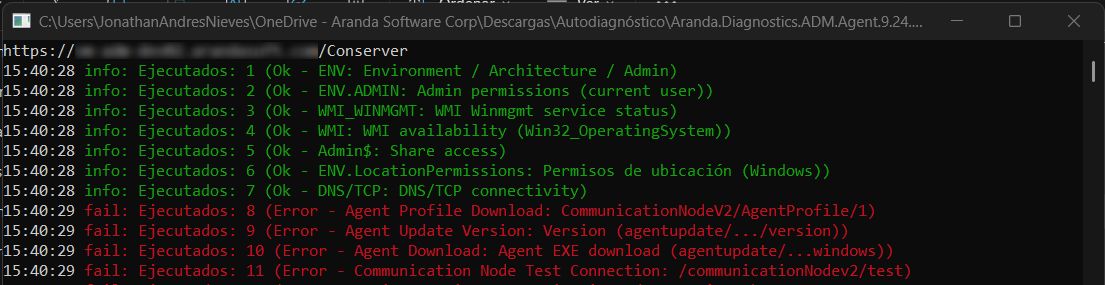
It can occur due to a communication failure with the node to which the diagnostic test is being performed, it is recommended to check that the service is operational or verify the firewall rules.
13. Device Registration
A request is made to the console to perform a test registration with random data and verify that the devices can be registered correctly in the console.
{
"TestId": "RegisterDevice",
"Group": "Inventory.CommunicationNode",
"Name": "CommunicationNodeV2 Register",
"Status": "Ok",
"Findings": [],
"Evidence": {
"PayloadResource": "Aranda.Diagnostics.ADM.Agent.Core.Assets.register-body.json",
"RunGuid": "c164570f229b4858ba240895c092b107",
"DeviceName.Original": "TestArandaDiagnosticsAgent",
"DeviceName.Final": "TestArandaDiagnosticsAgent-c164570f229b4858ba240895c092b107",
"HwHash.Final": "c164570f229b4858ba240895c092b107",
"Url": "https://DNS-NAME/Repserver/communicationNodeV2/register",
"TimeoutMs": "30000",
"StatusCode": "200",
"ElapsedMs": "1322",
"Response.Token": "{E79387D5-CA80-4FA7-A404-3ADD4D4B7D42}",
"Response.Topic": "device/{FF2D3566-1474-4714-9DC3-6BC9F2F87266}",
"Response.BrokerPort": "1884",
"Response.BrokerIp": "IP-DETECTED",
"Response.Guid": "{FF2D3566-1474-4714-9DC3-6BC9F2F87266}",
"IsEnableServerNotification": "False"
}
}
⚐ Note: Once the self-diagnostic tests are finished, it is recommended to delete the test record(s) created in the console, depending on the number of executions of the utility. If there are multiple records, you can delete them by filtering by status No inventory and agent 9.12.2110.106 and then go to More options > All and then Remove devices.
14. Operation Verification Remote Administration
In this case, there are two paths:
-
LAN Remote Management: If the EnableServerNotification is set in True, a connectivity test is performed on the station verifying if port 9025 is available for use and that another program or service is not using it; If the agent is already installed, verify that the port is associated with the agent’s process and that it is in listen-only mode.
{ "TestId": "LOCAL.9025", "Group": "Inventory.RemoteAdmin", "Name": "Local port 9025 listening", "Status": "Ok", "Findings": [], "Evidence": { "Port": "9025", "Target": "localhost", "AgentService.Name": "ArandaAgent9", "AgentService.Exists": "True", "AgentService.Status": "Running", "AgentService.StartType": "Automatic", "AgentProcessPid": "6552", "AgentProcessName": "Aranda.Agent.ACOREService", "Port.ListenerCount": "2", "Port.Bindings": "0.0.0.0, ::", "Port.Listening": "True", "PortOwnerPid": "6552", "PortOwnerProcessName": "Aranda.Agent.ACOREService", "Port.OwnerMatch": "True (PID 6552)", "ConnectedIP": "127.0.0.1" } }
Example of error:
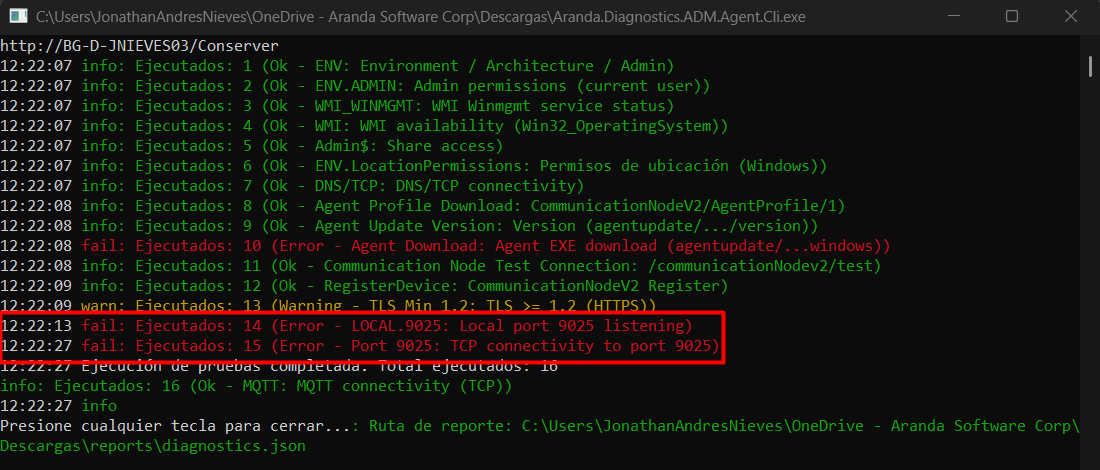
If you have the agent installed, check from the Network > Resource Monitor > Listening Ports that the Aranda.Agent.ACOREService.exe process is running on port 9025. Validate that in the Firewall Status say Allowed, not restricted; otherwise, check the firewall rules.
-
Remote Management Outbound Connection: If the EnableServerNotification is set in True, a request is made using the WebSocket protocol to the site identified in the registration procedure (Step 14). The utility verifies that the plugin is installed and that the site is secured by HTTPS.
{ "TestId": "Notifications WebSocket", "Group": "Inventory.RemoteAdmin", "Name": "Repserver notifications WebSocket(webhub)", "Status": "Ok", "Findings": [], "Evidence": { "BaseUrl": "https://DNS-NAME/repserver/notificationmessage", "Host": "DNS-NAME", "Scheme": "https", "WsUrl": "wss://DNS-NAME/repserver/notificationmessage/webhub", "ElapsedMs": "7903", "State": "Open" } }
Example of error:
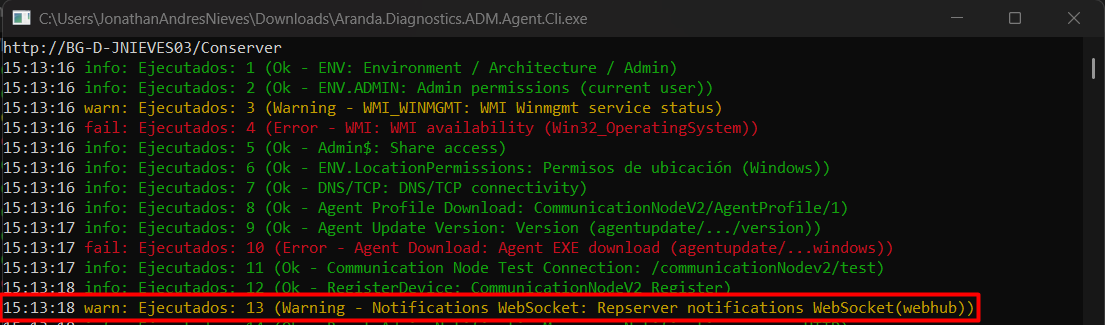
The most common causes for this error can be:
- The lack of HTTPS configuration on the node that is being diagnosed. For more information, please consult the following links according to your infrastructure:
- The lack of the WebSocket component in roles and features.
15. Site Notification Verification
A check is performed on the Repserver/notificationmessage site verifying that it is available and capturing response times.
{
"TestId": "RemoteAdmin NotificationMessage",
"Group": "Inventory.RemoteAdmin",
"Name": "Notificationmessage HTTP",
"Status": "Ok",
"Findings": [],
"Evidence": {
"BaseUrl": "https://DNS-NAME/repserver/notificationmessage",
"Method": "GET",
"StatusCode": "200",
"ElapsedMs": "684",
"ContentType": "text/html"
}
}
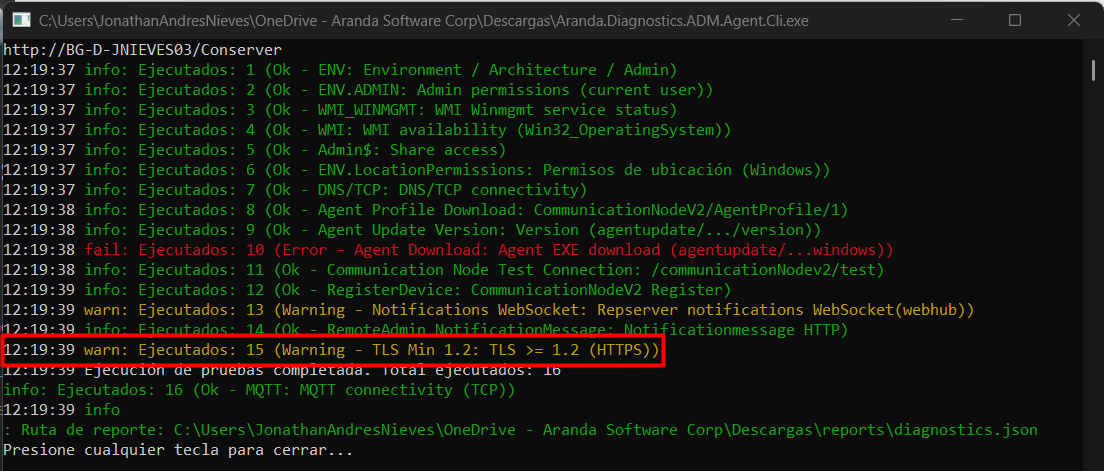
16. Minimum TLS verification
A verification of the TLS cryptographic protocol handled by the site that is being targeted to perform the diagnostic test is performed.
{
"TestId": "TLS Min 1.2",
"Group": "Inventory.RemoteAdmin",
"Name": "TLS >= 1.2 (HTTPS)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"RepserverUrl": "https://DNS-NAME/Repserver",
"Scheme": "https",
"Host": "DNS-NAME",
"Port": "443",
"ElapsedMs": "161",
"NegotiatedProtocol": "Tls13",
"CipherAlgorithm": "Aes256",
"CipherStrength": "256",
"HashAlgorithm": "Sha384",
"HashStrength": "0",
"KeyExchangeAlgorithm": "None",
"KeyExchangeStrength": "255"
}
}
Example of error:
Verify that the server meets the minimum requirements, such as the minimum supported version of TLS (1.2). For more information, see the note Things to keep in mind Requirements.
17. MQTT/IOT Stock Submission Component Verification
First, a verification test is carried out to validate if the parameter is configured DeviceMessageConfiguration, if such a configuration exists, a connectivity test to the MQTT is performed using the DNS/IP and port configured in that component.
{
"TestId": "ENROLLMENT",
"Group": "Inventory.CommunicationNode",
"Name": "Device enrollment (POST /api/device/enrollment)",
"Status": "Ok",
"Findings": [],
"Evidence": {
"Url": "https://DNS-NAME/Repserver/api/device/enrollment",
"RequestBody": "{\"guid\":\"{4BE52D7A-5B13-4B59-8621-C39D92A9FA36}\",\"version\":\"9.24.1.3\",\"sufix\":\"ADM\"}",
"StatusCode": "200",
"ResponseBody": "{\"metaData\":\"{\\\"broker\\\":\\\"IP-DETECTED\\\",\\\"password\\\":\\\"\\\",\\\"port\\\":1884,\\\"secure\\\":false,\\\"sslProtocols\\\":0,\\\"topic\\\":\\\"ADM_4BE52D7A-5B13-4B59-8621-C39D92A9FA36\\\",\\\"username\\\":\\\"\\\"}\",\"type\":1}",
"Response.TypeValue": "1",
"Response.MetaData": "{\"broker\":\"IP-DETECTED\",\"password\":\"\",\"port\":1884,\"secure\":false,\"sslProtocols\":0,\"topic\":\"ADM_4BE52D7A-5B13-4B59-8621-C39D92A9FA36\",\"username\":\"\"}",
"Response.TypeName": "MQTT",
"Source": "Enrollment",
"Enrollment.Broker": "IP-DETECTED",
"Enrollment.Port": "1884",
"Enrollment.Topic": "ADM_4BE52D7A-5B13-4B59-8621-C39D92A9FA36",
"Probe.Broker": "IP-DETECTED",
"Probe.Port": "1884",
"Probe.Topic": "ADM_4BE52D7A-5B13-4B59-8621-C39D92A9FA36",
"Probe.MQTT.TcpConnect": "Ok"
}
}
⚐ Note: In the current version, it is not possible to perform a connectivity test to the IOT component that is configured for DeviceMessageConfiguration.
If the parameter does not exist DeviceMessageConfiguration, validates whether MQTT is configured in the Web.config of the node being tested and performs a connectivity test using the DNS/IP and port configured on that component.
{
"TestId": "ENROLLMENT",
"Group": "Inventory.CommunicationNode",
"Name": "Device enrollment (POST /api/device/enrollment)",
"Status": "Ok",
"Findings": [
{
"Code": "ENROLL.BAD_STATUS",
"Message": "Respuesta no exitosa en enrollment.",
"Severity": "High",
"Details": "\"DeviceMessageConfiguration_NotFound\""
},
{
"Code": "ENROLL.FALLBACK.BAD_STATUS",
"Message": "Enrollment falló. Se intenta MQTT usando la configuración registrada.",
"Severity": "Low",
"Details": null
},
{
"Code": "ENROLL.FALLBACK_MQTT_OK",
"Message": "Falló enrollment, pero la prueba MQTT con la configuración registrada fue exitosa.",
"Severity": "Low",
"Details": null
}
],
"Evidence": {
"Url": "https://DNS-NAME/Repserver/api/device/enrollment",
"RequestBody": "{\"guid\":\"{0DCFB561-7A61-48DF-A7F1-BD5102A16362}\",\"version\":\"9.24.1.3\",\"sufix\":\"ADM\"}",
"StatusCode": "409",
"ResponseBody": "\"DeviceMessageConfiguration_NotFound\"",
"Fallback.Source": "RegisterCommunicationNode",
"Fallback.Broker": "IP-DETECTED",
"Fallback.Port": "1884",
"Fallback.Topic": "device/{0DCFB561-7A61-48DF-A7F1-BD5102A16362}",
"FallbackProbe.Broker": "IP-DETECTED",
"FallbackProbe.Port": "1884",
"FallbackProbe.Topic": "device/{0DCFB561-7A61-48DF-A7F1-BD5102A16362}",
"FallbackProbe.MQTT.TcpConnect": "Ok"
}
}
Example of error:
Check the firewall rules for any restrictions on the IP or DNS configured for the MQTT component by port 1884 or validate that the MQTT service on the server is operational.
18. Inventory Shipment Verification
A test file is loaded to the storage path configured for the node being diagnosed.
{
"TestId": "UploadFileV2",
"Group": "Inventory.CommunicationNode",
"Name": "CommunicationNodeV2 UploadFileV2",
"Status": "Ok",
"Findings": [],
"Evidence": {
"PayloadFileName": "test_Aranda_diagnostics_agent.txt",
"Url": "https://DNS-NAME/Repserver/communicationNodeV2/uploadfilev2",
"Method": "POST",
"MultipartField": "inputStream",
"FileName": "test_Aranda_diagnostics_agent.txt",
"FileBytes": "75",
"TimeoutMs": "30000",
"StatusCode": "200",
"ElapsedMs": "395",
"ResponseLength": "2"
}
}
⚐ Note: Once the self-diagnostic tests are finished, it is recommended to delete the test file(s) created in the storage path that is configured for the node that was performed, these files are stored in the folder Exception
Example of error:
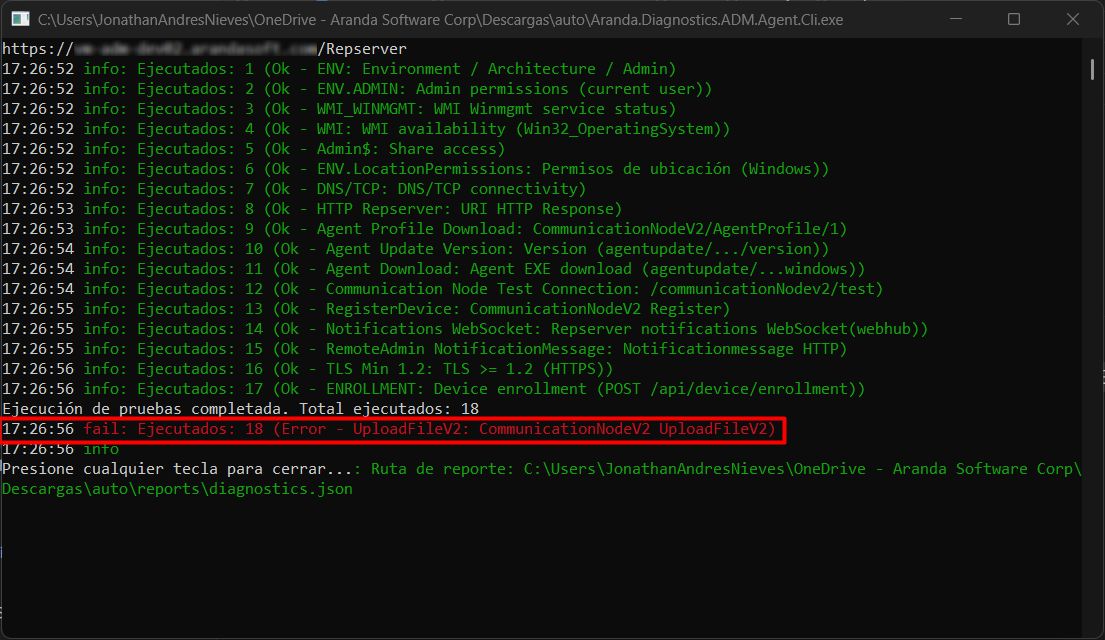
The most common causes for this error can be:
- You don’t have a valid local file storage path or blob storage configured for the node you’re targeting. For more information, see Communications
- You don’t have read and write permissions on the local file storage path or blob storage that you have configured for the node you’re targeting.
In the following link you can find the executable of the self-diagnostic agent Self-Diagnostic Agent


